Stop AI Agents fromRunning Wild
Give your agents identity and limits. Shield your tools and services from unauthorized access. Every decision signed and verifiable. Power agent-to-agent commerce with signed terms and cryptographic receipts.
No credit card required.
Built for Both Sides of the Agent Stack
Whether You Deploy Agents or Host What They Access
If You Deploy AI Agents
Your agents are making API calls, accessing data, and spending money on your behalf. Without trust infrastructure, you have no way to know what they're doing — and no way to stop them when they go wrong.
Modei gives every agent a cryptographic identity with built-in limits. You define what's allowed, and the infrastructure enforces it — before damage is done, not after.
If You Run APIs, MCP Servers, or Tools
You're exposing APIs and services to AI agents you didn't build and don't control. You need to verify who's calling, what they're allowed to do, and optionally meter and bill for usage.
Modei lets you require cryptographic proof of identity and authorization on every request — and gives you the metering and settlement infrastructure to monetize agent access.
Start in Minutes, Not Sprints
Register Your Identity
Create your account on Modei and generate cryptographic credentials for your agents or your services.
Issue Passports or Create Gates
Deploying agents? Issue passports with scoped permissions. Hosting services? Create gates that define what’s allowed.
Connect via MCP or API
Plug in with the TypeScript or Python SDK. Modei is MCP-native — it works with Claude, GPT, and any MCP-compatible host.
Every Action Signed & Verified
From this point forward, every agent request is verified, every decision is signed, and every action is recorded.
Integrate in Minutes
Whether you're deploying agents or protecting services, Modei plugs into your stack with a few lines of code.
{ "mcpServers": { "modei": { "command": "npx", "args": ["modei-mcp"], "env": { "MODEI_API_KEY": "mod_live_xxxxxxxx" } } }}Six Pillars of Trust
Passports
Cryptographic identity bound to what the agent actually is — model, version, architecture. Not just who operates it. Issue in seconds. Verify in under a millisecond. Delegate with guaranteed attenuation.
Learn more about PassportsGates
Policy enforcement where it matters — between the agent and the resource. Permission catalogs, spend limits, rate controls, domain allowlists. Credentials pinned to specific catalog versions so terms can’t change without your awareness.
Learn more about GatesEnforcement
Decisions made before damage is done. Spend limits enforced at the gate, not tracked after. Revocation propagated in real time, even mid-execution. Three-decision model: permit, block, or suspend.
Learn more about EnforcementSupravision
Human oversight when it matters. When an agent hits a decision that needs a human, you get an SMS. Reply YES or NO directly from your phone — no app required. Emergency stop from the dashboard. Every approval recorded as a signed attestation.
Learn more about SupravisionAudit
Every action produces a signed receipt. Every receipt is hash-linked to the last. Both sides hold a copy. Gaps are detectable. Tampering is evident. Export the whole chain for compliance, accounting, or regulatory review.
Learn more about AuditCommerce
Infrastructure for agent-to-agent transactions. Services publish signed catalogs with pricing and terms. Agents discover, compare, and transact — with pricing locked to their credential and every transaction producing a cryptographically verifiable receipt.
Learn more about CommerceEmpower Commerce Between Agents and Services
Infrastructure for agent-to-agent commerce. Publish services, negotiate terms, meter usage, and settle transactions — all with cryptographic proof.
Publish Service Catalogs
Define what your service offers, what it costs, and what permissions are required. Agents discover your terms before they connect.
Bilateral Metering
Both sides of every transaction maintain independent usage records. Disputes are resolved by comparing cryptographically signed meter readings.
Enforced Spend Limits
Agents can’t exceed budgets. Spend caps are enforced at the gate, not just tracked after the fact. Overages are blocked before they happen.
Signed Settlement Receipts
Every transaction produces a cryptographically signed receipt that both parties can independently verify. No he-said-she-said.
Commerce Flow
How an agent-to-agent transaction works, end to end.
- 1Discover
Agent discovers service catalog and terms
- 2Authorize
Agent presents passport with spend authorization
- 3Verify
Gate verifies credentials and enforces limits
- 4Deliver
Service delivered, usage metered bilaterally
- 5Settle
Signed receipt issued to both parties
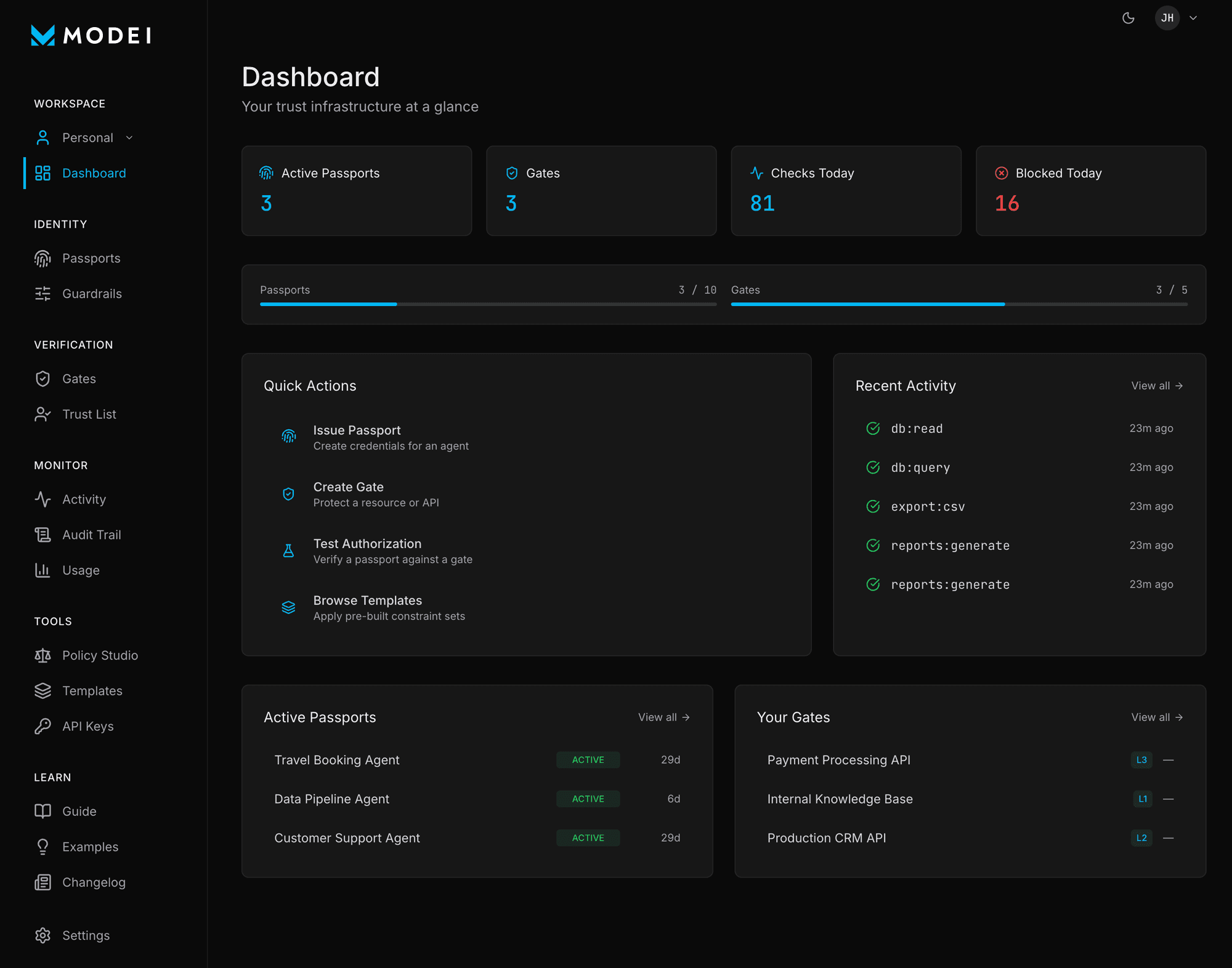
Your Trust Infrastructure at a Glance
Issue passports, configure gates, enforce guardrails, and monitor every agent action, all from one dashboard.
Simple, Transparent Pricing
Start free. Scale when you're ready.
Free
For testing and personal projects
- 3 gates
- 5 passports
- 1k decisions/mo
Pro
For teams running agents in production
- 20 gates
- 100 passports
- 50k decisions/mo
Teams
For teams managing many agents and services
- Unlimited gates & passports
- 500k decisions/mo
- Up to 15 seats
No credit card required.
Your Agents Are Already Out There. Govern Them.
Deploy trust infrastructure in minutes. Free to start. No credit card required.